The Justice for Prosperity foundation (JfP) is investigating potential interference and intimidation during the 2026 municipal elections. Since 2022, elections have been targeted with disinformation spread through so-called Doppelgänger websites, fake copies of major media outlets such as Bild and The Guardian. More recently, the same method was deployed during elections in Germany (2025) and the United States (2024). JfP therefore investigated whether Dutch media organisations face the same threat. The findings show that while many precautions are already in place, significant vulnerabilities remain.
The municipal elections take place on 18 March. Protecting the integrity of that democratic process matters. International experience and research consistently show that malicious actors attempt to manipulate elections. One method they use is spreading disinformation through Doppelgänger websites. A recent example is the Russian influence operation targeting the German federal elections of February 2025.
To find out whether the Dutch municipal elections are being targeted in the same way, JfP conducted a systematic internet scan for Doppelgängers of major news outlets.
What are Doppelgänger websites?
A Doppelgänger website is a convincing copy of a legitimate website, deliberately designed to mislead visitors. The name fits: just as a doppelgänger looks strikingly like another person, these sites mirror the real thing closely enough to deceive. Visitors see a familiar layout, a recognisable logo and credible headlines, but the content is fabricated or distorted.
The method is straightforward. A malicious actor registers a domain name that closely resembles that of a reputable newspaper or broadcaster: a small typo (for example “telegraav.nl” instead of “telegraaf.nl”), an added word (“telegraafmedia.nl”) or an alternative extension (“.com”). The site is then filled, in part or entirely, with articles that present political lies or misleading information as genuine news.
Why this matters for elections
The threat is not theoretical. Since May 2022, a large-scale operation has been spreading disinformation through Doppelgängers of at least seventeen media organisations, including major outlets such as Bild, The Guardian and Le Monde. These campaigns have targeted multiple countries across multiple election cycles. Germany, France and Ukraine have all been targeted. Around the European Parliament elections of June 2024, researchers documented large waves of attacks with country-specific disinformation.
The method has been used outside Europe too. Around the 2024 US presidential elections, Doppelgängers of American news websites targeted specific population groups with tailored disinformation. Articles on these sites spread through social media, where a domain name that looks legitimate at first glance is enough to generate mass sharing.
This form of disinformation could also be deployed during the municipal elections, through Doppelgängers of local and regional media. Smaller in scale per outlet, but more dispersed and harder to trace than attacks on national media.
JfP's approach
Detecting both large-scale and dispersed small-scale disinformation calls for a broad, fine-grained approach. JfP developed an automated scanning method to identify suspicious domains systematically. The method draws on technical reports from earlier Doppelgänger operations in Europe and combines automated domain analysis with manual verification.
In the first phase, JfP generates large numbers of potential domain variants based on the official domain names of various news outlets. These are automatically checked for activity and filtered using multiple technical and content-based indicators. Each remaining domain receives a risk score.
In the second phase, the system flags the most notable domains for a human analyst, who manually assesses whether a website should be classified as potentially dangerous. Automated systems handle scalable filtering well, but the final judgement requires human reasoning and contextual understanding. That combination is what makes Doppelgänger detection reliable.
Room for improvement
Countering Doppelgänger websites requires more than detection. News organisations also need effective defensive strategies, starting with registering domain variants of their own names. Equally important is anticipating typosquatting: malicious actors who register domains with minor spelling errors, then use them either to harvest credentials and personal data from visitors who land there by accident, or to spread disinformation.
JfP’s research shows that several news organisations have taken good first steps, but many have yet to mount an optimal defence.
The NOS has registered nos-nieuws.nl and a number of other variants, yet several variants remain unclaimed. This shows real awareness of the issue, but further steps are warranted. JfP also found that third parties have registered a number of NOS-adjacent URLs. The NOS would do well to monitor these and consider acquiring them.
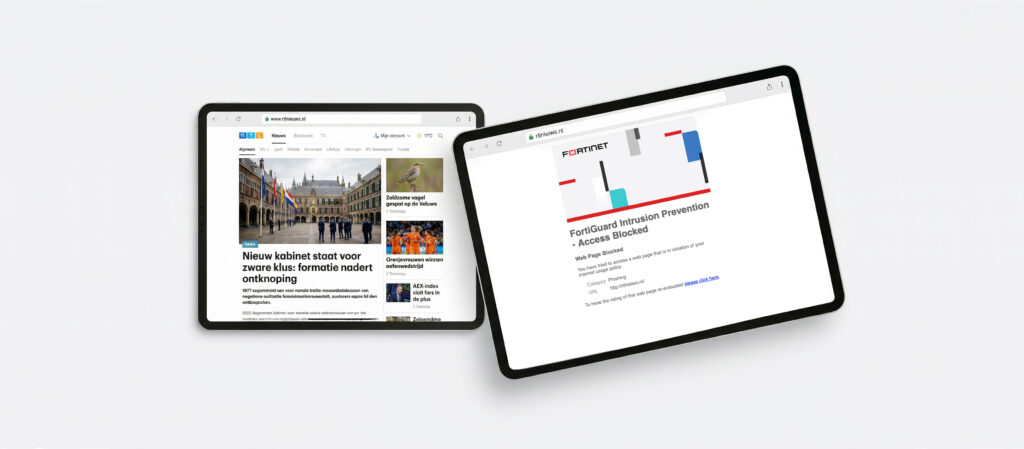
Around RTL Nieuws, JfP found a concerning instance of typosquatting. The domain rtlnieiws.nl, a typo that could easily occur when typing the official rtlnieuws.nl, is in the hands of an actor who manages multiple typosquat websites across different brands and sectors. JfP advises against visiting rtlnieiws.nl directly. The site appears empty: no news articles, no visible content. What it does contain is a hidden script designed to collect data from visitors who land there by accident. This is most likely financially motivated data harvesting. While it does not fit the profile of a classic political Doppelgänger operation, the find underlines a broader point: the landscape around unclaimed media domain variants is not empty. It is actively exploited, in this case by an actor primarily interested in financial fraud rather than disinformation.
Best in class: De Telegraaf
Doppelgänger campaigns tend to target media that are critical of EU policy or government intervention, in JfP’s experience at least. That makes them a credible vehicle for spreading disinformation to audiences already sceptical of official narratives. Against that backdrop, it is reassuring that the publisher of De Telegraaf has its domain security well under control. JfP found a large number of domains closely resembling telegraaf.nl, all of which redirect visitors to the official website. Addresses such as telegraafonline.nl, telegraaf-media.nl and even telegraaaf.nl (with three a’s) all lead to the real Telegraaf site.
Claiming these domains is an effective defensive strategy. Controlling the most obvious variants denies malicious actors the opportunity to exploit them. De Telegraaf has not only registered the variants, it has also set up redirects to the official site. The redirects are unrelated to the disinformation threat as such, but they are smart practice regardless.
Conclusion and recommendations
JfP’s investigation ahead of the 18 March 2026 municipal elections found no active Doppelgänger websites demonstrably spreading political disinformation. That is good news. The other findings, however, show that the landscape around unclaimed domain variants is open to exploitation. From financially motivated data harvesting to ready-to-launch fake news platforms: the risk is real.
News organisations should systematically map which variants of their domain names remain unclaimed. The highest-risk variants warrant registration, followed by a working redirect to the official site. For the general public and for journalists: always check the exact URL before sharing an article. A near-correct domain name is often the only visible sign that you have landed on a fake site.
The Justice for Prosperity foundation will continue to monitor the Dutch information environment in the run-up to 18 March 2026. Reports of active Doppelgänger websites can be submitted through JfP’s channels. JfP will of course share its findings directly with the organisations concerned, including the NOS, De Telegraaf and RTL.